Hello again people,
A couple of days ago I successfully passed the OSCE exam, So I wanted to share with you my experience and my mistakes may be it can be helpful.
Unlike OSCP which provided you with many labs and challenged you to hack them, OSCE provides you the labs to practice so everything you need to do in the labs is explained fully in the videos and the pdf file.
Some people find this less interesting than OSCP since there’s no challenge in following a video and they might be right but I think the main goal was to make you comfortable with exploit development topics such as bypassing ASLR, using egg hunters ,etc ….
For me I already knew most of the techniques described so I am not gonna lie to you and say that I practiced all the labs because I didn’t.
In the exam I realized that was a mistake because there was one of the topics explained in the course (I can’t say what exactly since it will reveal a question in the exam) that I saw in the video and thought it was easy since I understood it but in the exam it consumed some of my time because even though it was understandable and easy to follow, it was very time consuming in practice specially if it’s the first time you do it.
So my advice to you is to follow and do everything in the labs even if you have a prior knowledge of it.
The exam was 48 hours so you need to do some time management regarding the tasks and also how you’re gonna sleep.
Since we live in our beloved Egypt prepare yourself to keep it calm when the internet connectivity goes down, and also when your backup plan (3G or even 4G).
In general to pass this exam you need to be good at exploit development and also know how do post exploitation for web applicatitons (mainly turning web vulnerabilities into RCEs), also you might need knowledge about privilege escalation.
My comment about the exam is that it was easy but some tasks took some time to solve especially if you made a mistake (for example producing a bad character in your encoder).
At last I want to share with you some of specific topics you need to be good at to pass the exam based on the challenges in my exam:
- A good understanding of assembly language.
- Understanding how to write simple shell code.
- Understand how to manually write a custom encoder.
- How to work with a debugger in an efficient, fast way (they use ollydebug).
- Try to make you’re self comfortable with the debugger, try to make it you’re second home :).
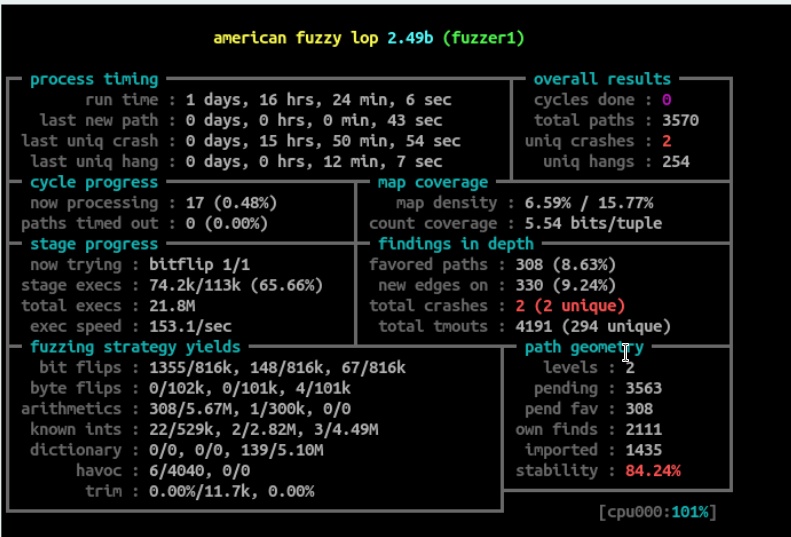
- A good knowledge about fuzzing.
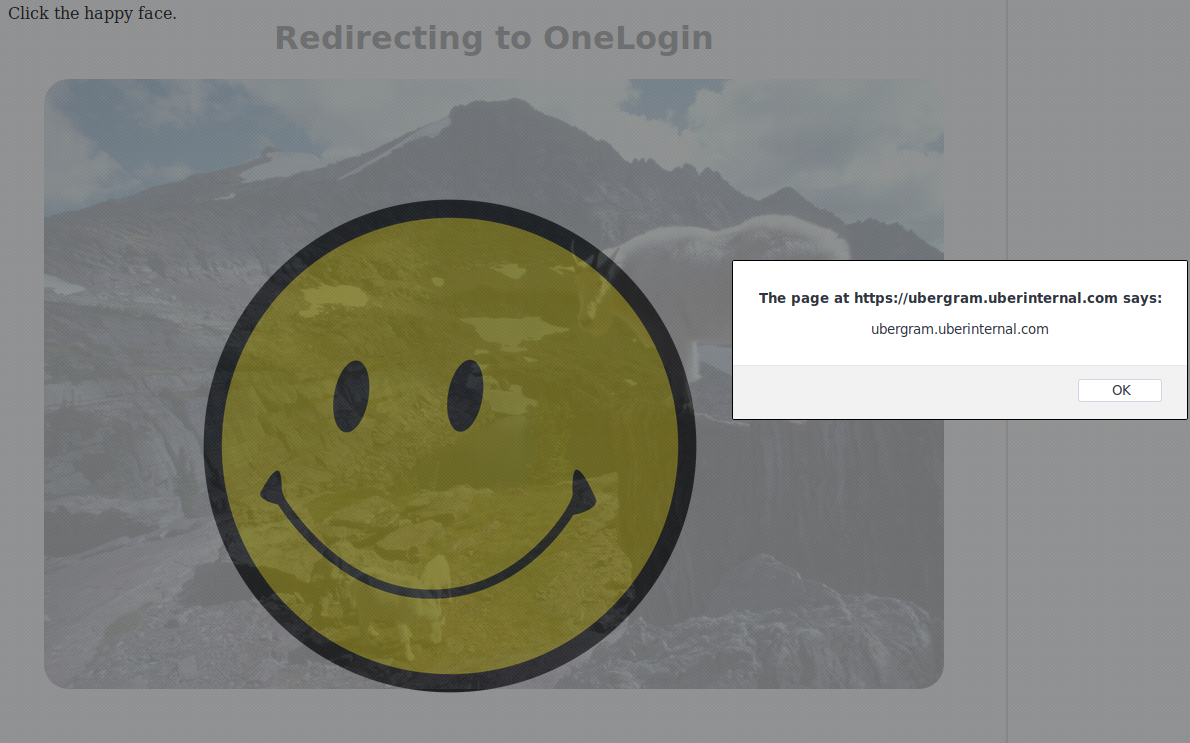
- Methods for getting shell from web vulnerabilities (XSS,RFI,LFI, SQL injection … etc).
- How to manually encode an exe to bypass antivirus.
- How to manually inject your code into an exe.
Don’t worry most of the topics above are explained in the course, my advice is to study the course and then come back to the above topics and see if there’s any of them that you don’t fully understand.
Even though those topics are explained in the course, in the exam it’s a little bit different for example I encoded the exe by following exactly the steps described in the course and it was still detected by the AV so you need to have some tricks of your own.
And finally .. Never give up and try harder.