So, the NSA decided to release their reverse engineering tool named Ghidra, I did have some time to play with it, and to be honest I was really impressed it's an awesome tool, however there are some problems that I encountered when using the tool.
The Good
There are so many things that are good about ghidra, the tool is completely free and have some features that doesn't even exist in commercial products.
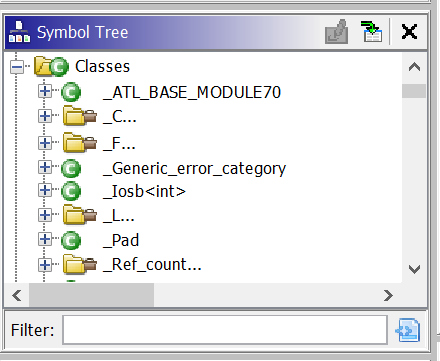
The most interesting feature is the de-compiler, it works in a way similar to a godbolt.org, this feature allows you to select certain parts of assembly and the tool will highlight their corresponding representation in the decompiled C source code, this is a very cool feature for beginners in reverse engineering.
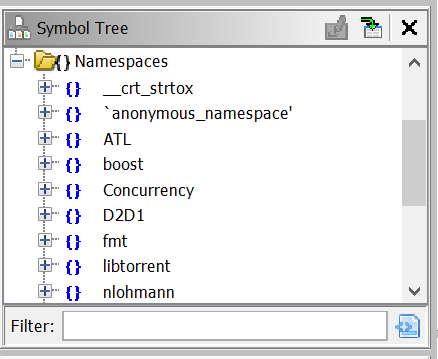
Another cool feature that I found to be very interesting is the fact that Ghidra can actually can detect some of the namespaces and classes, unlike ida pro which requires skills and/or plug-ins to do that task as far as I know, and assuming that a class wasn't automatically detected you can define a class and then drag and drop functions to that class, this is amazing and allows a much better work flow, the class name is reflected in the disassembly window so later any calls to member functions of a class will be spotted easily.
One more thing you can do is that you can enable the Function call tree window which will show both incoming and outgoing calls to and from this function.
If you want to know information about a function just click on its name and all the windows including the disassembly, code window, call tree and function graph will be updated to that function.
A good thing is that you can have all these windows open at the same time without any tabs (you can still use tabs if you wish).
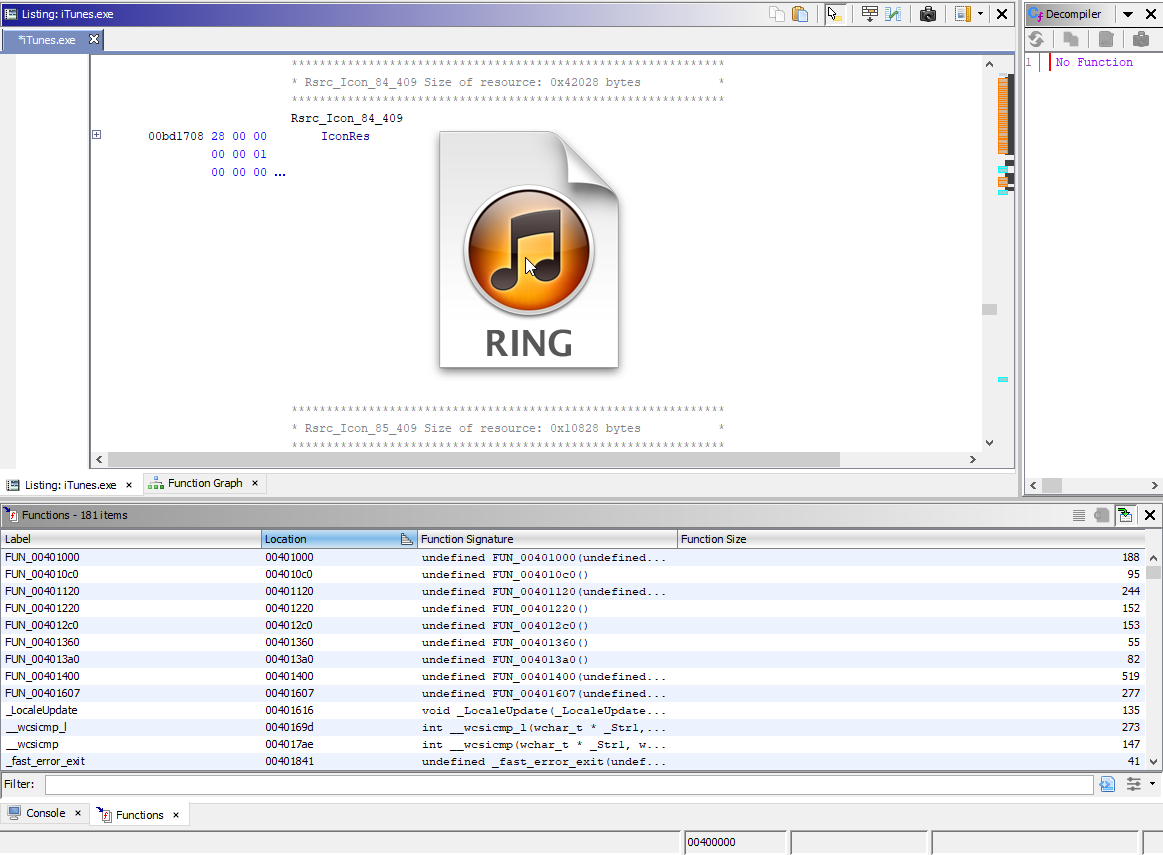
Update : after writing this article I found a cool feature that is very useful, Ghidra actually detects files embedded in the file you're analyzing, this means that if there's an image or icon in the resources section, you will find it displayed right into the assembly listing window .. isn't that amazing?
The Ugly
So the tool is perfect .. right?
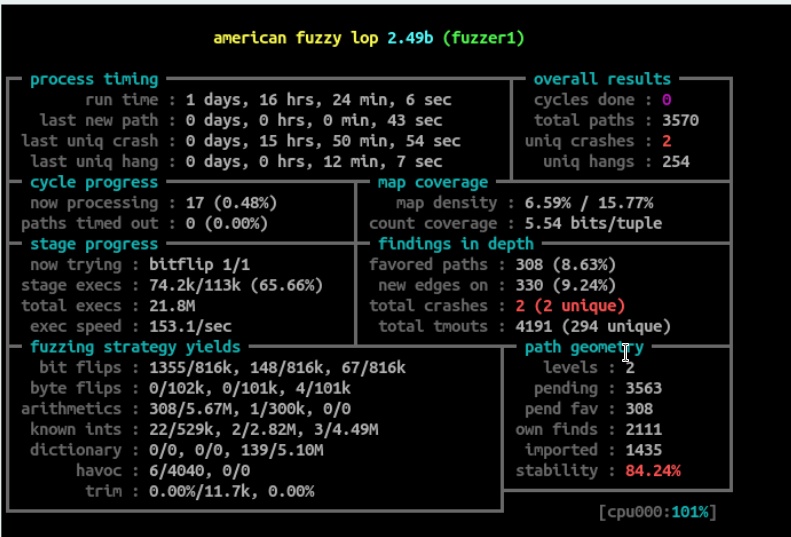
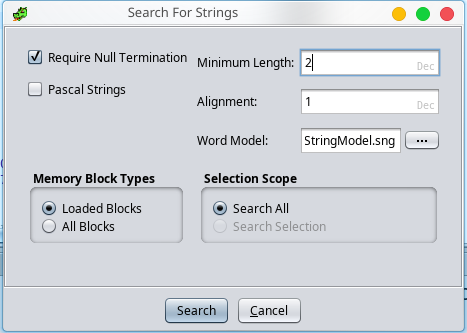
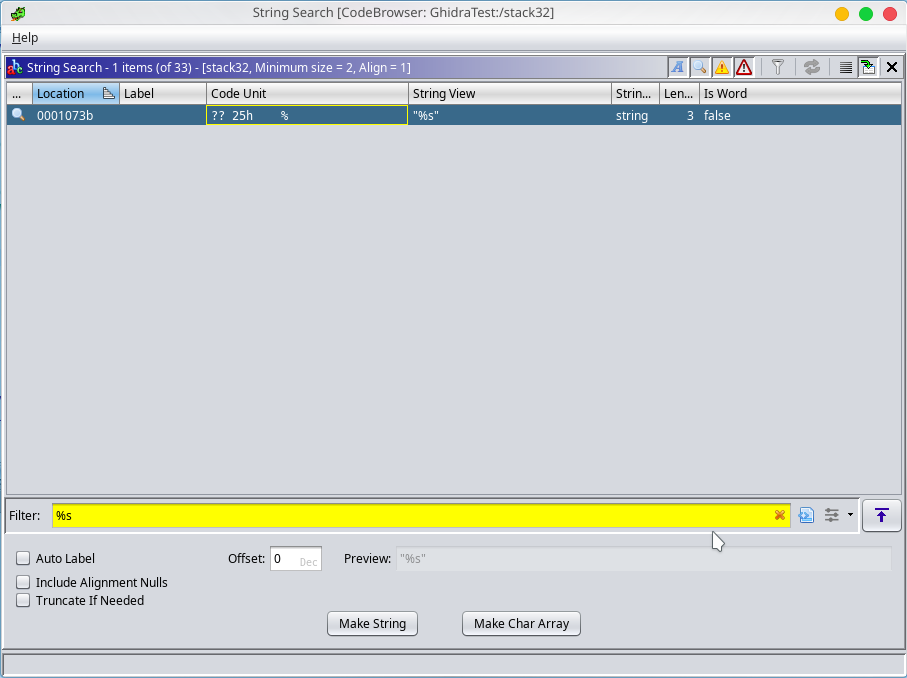
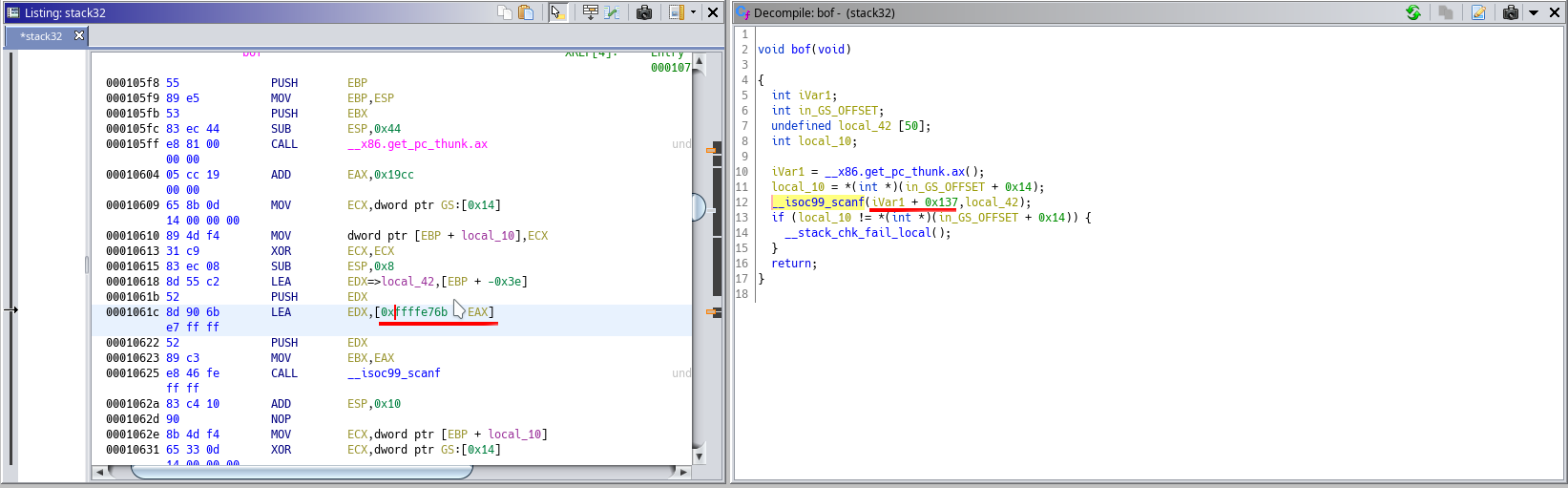
Well, sadly nothing in life is perfect, my first encounter with the tool was a bad one, I had an executable that I compiled for x86, this was the first elf file I tried to decompile with Ghidra, sadly it did a bad job decompiling it, the file contained a call to scanf and the first argument is simply %s, the fact that this is only 2 characters is important because by default the minimum string length is set to 5 by default, so by default this string is not going to be recognized because it's only 2 characters, so what I did is that I went to search menu then I chose strings and I set the minimum size to 2 as seen in the screenshot.
I clicked search and now I can find the %s which is nice.
So problem solved .. well, not really I found the string and I did change the type to string, however the bad part is that the tool still wasn't able to find any references to that string, also in the function itself I couldn't find the string used by scanf, you can see in the screenshot below that it couldn't find the references to the string.
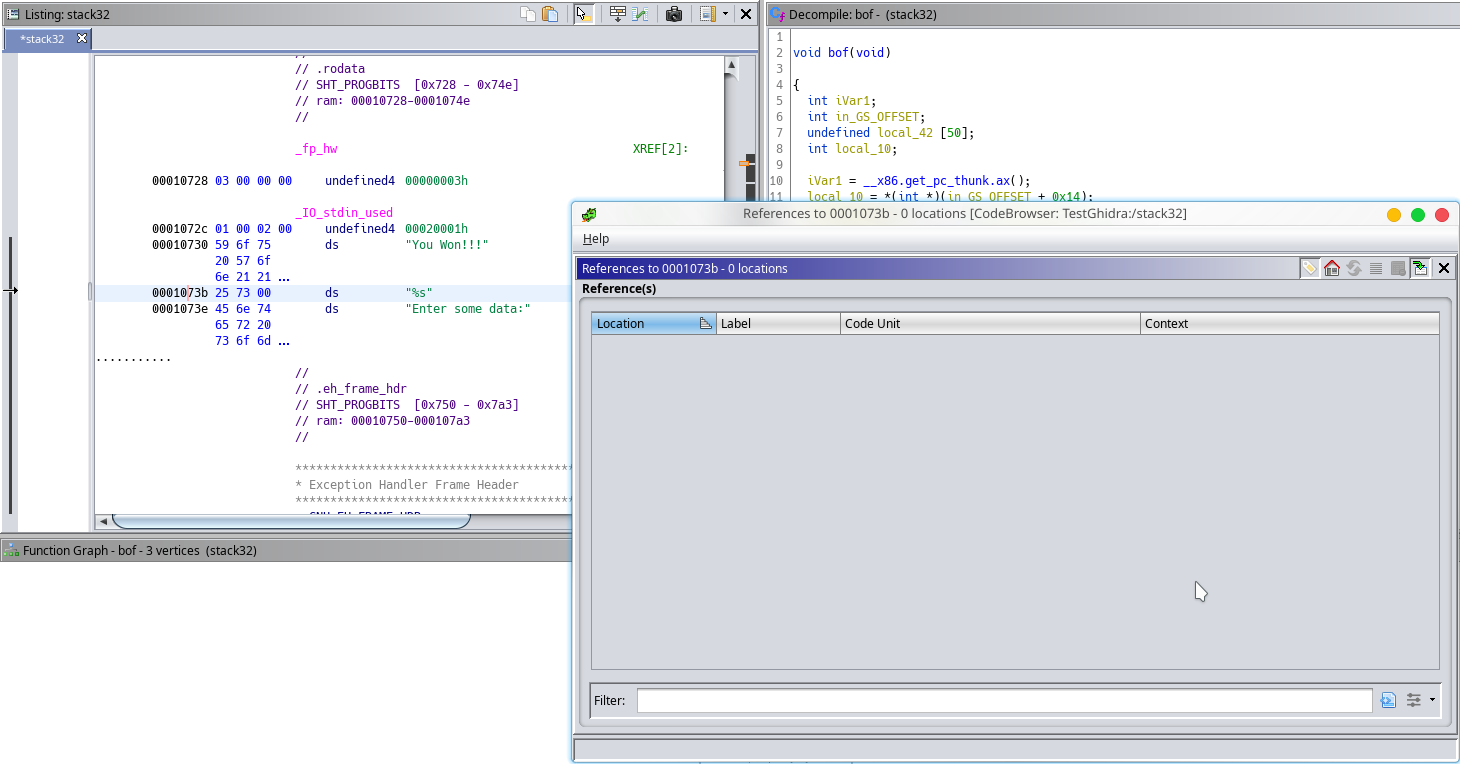
Also, in the function itself, when you double click the address it says that the address is invalid and not in the program memory ..
I used IDA pro and it was able to detect the string right away.
I compiled the same code as elf x64 and it was able to find the string and the decompiled code actually showed scanf("%s" which is cool, I also compiled it for windows x86 and it worked fine so the problem happened only with x86.
A Piece of Advice
I am not saying that Ghidra is bad as a matter of fact I think Ghidra will be my choice for any future RE projects.I have seen similar failures with IDA and Radare 2 so it's not a Ghidra specific problem but what I am saying is you shouldn't always trust the tools and always assume that they might make a mistake.
Most of the times I don't rely on one tool for reversing since may be one of the tools mis-interpret something important in the code which will at least get you confused and waste your time to figure out the mistake.
For example, in the case where a string was missing for example since I created the file for testing, I knew that the string existed, however if I didn't it would have taken so much time to figure it out using only one tool but when opening the file in IDA everything looks normal and the strings are correctly interpreted.